 https://www.ikarussecurity.com/wp-content/uploads/2023/05/ransomware-2.jpg
338
600
IKARUS
https://www.ikarussecurity.com/wp-content/uploads/2026/02/IKARUS-Security-Logo-2.png
IKARUS2026-04-28 09:39:482026-04-28 09:41:39Ransomware is changing: from encryption to data Theft
https://www.ikarussecurity.com/wp-content/uploads/2023/05/ransomware-2.jpg
338
600
IKARUS
https://www.ikarussecurity.com/wp-content/uploads/2026/02/IKARUS-Security-Logo-2.png
IKARUS2026-04-28 09:39:482026-04-28 09:41:39Ransomware is changing: from encryption to data Theft19. May, 2021
At the end of April thousands of QNAP users were hit by a ransomware attack. The hackers used an exploit to encrypt all the files on the NAS drives with 7-zip using a 32 character long key for an AES encryption. As ransom they wanted 0,01 Bitcoins, about 500 Dollars. Some were lucky, but some of the victims paid the ransom, but got no key to decrypt their files. In the meantime the amount was tripled to 0,03 Bitcoins.
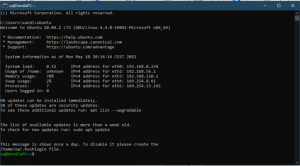 Two Austrian security experts analyzed the method the hackers used and found out, that they made the mistake to delete the original files after encryption. So by undeleting the files on the ext4 partition you get most of your files back, but sadly with no meaningful names, without a directory structure and all with the same timestamp. What was needed, was a script that looks for the original names and timestamps. By matching the size and CRC32 of the original and the undeleted files most of the information is recoverable. But be aware that you will not get back all of your files!
Two Austrian security experts analyzed the method the hackers used and found out, that they made the mistake to delete the original files after encryption. So by undeleting the files on the ext4 partition you get most of your files back, but sadly with no meaningful names, without a directory structure and all with the same timestamp. What was needed, was a script that looks for the original names and timestamps. By matching the size and CRC32 of the original and the undeleted files most of the information is recoverable. But be aware that you will not get back all of your files!
Here is the writeup and the basic script to get the files back. In one instance it was able to recover about 90% of the files.
Source:

















