IKARUS anti.virus Portal
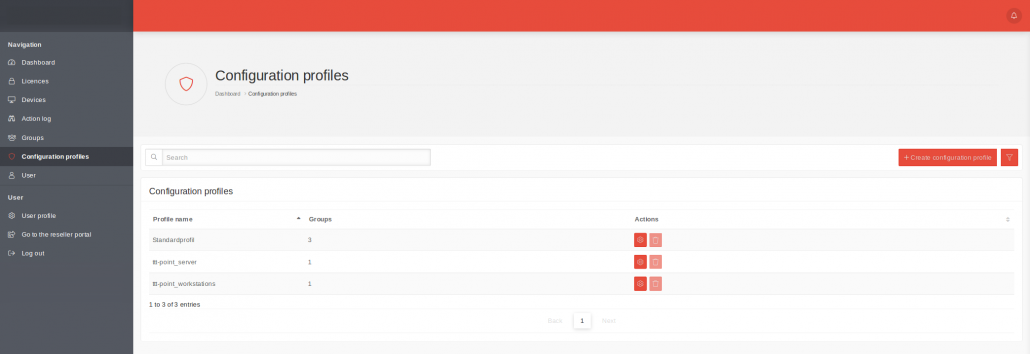
1 Overview of the Configuration Profiles
All existing configuration profiles are displayed in this menu. Here, configuration profiles can be edited, created or deleted.
Any number of configuration profiles can be created. This allows different areas, locations or departments to be mapped and differentiated.
2 Creating a Configuration Profile
2.1 Profile settings
| Caption | Description |
|---|---|
| Name | Free choice of name for the configuration profile. |
| Auto Synchronization | If the “Auto Synchronization” checkbox is selected in the profile settings of the configuration profiles, it is no longer necessary to roll out the initial configuration on AV clients manually. If clients are moved to other groups, the configurations must be pushed manually as before. |
| Owner | Firm, which is to have access to the profile can be selected as the owner. The assignment of the owner to a company determines who can use this configuration profile. When a configuration profile is created for a reseller (at the top of the group hierarchy), only that reseller has access to that profile. If a profile is created for a customer, this customer and the reseller can access the profile and define recipients for notifications.
|
2.2 MSI configuration
| Caption | Default | Description |
|---|---|---|
| Email Protection | on | Scans emails for malware & viruses |
| Spam protection | off | Checks emails for spam |
| Automatic Updates | on | Automatic verification and installation of new software updates and virus database updates |
| Update following installation | on | One-time virus database and software update after installation |
| Autoscan | off | This option can be used to configure an automatic scan. |
| Daily Scan | off | The scan is performed daily |
| Weekly Scan | Day of the week | The scan is performed once a week on that day. |
| Monthly Scan | dd | The scan is performed once a month on that day. |
| Scan type | Choice of | Only one preconfigured scan type can be defined. |
| Quick system check | checks the Windows installation directory.
Most computer malware on a Windows system is located in this directory.
|
|
| System partitions | checks the drive or partition on which the operating system is located.
This checks all archives, directories, folders, and files on the system partition.
|
|
| Entire computer | checks all drives of the local PC, including plugged in USB drives. | |
| Scan time | 17:00 | Time at which the scan is to be performed (17:00 if not specified) |
| Proxy IP address | ||
| Proxy Port | The port number must be between 1 and 65535. | |
| Proxy Athentification | off | If activated, the MSI user name and password will be requested during the download. |
Removal of the option to disable system protection in the configuration file
Accept the settings with Save
2.3 Exclusions
The following exclusions can be configured:
| Type | Parameter |
|---|---|
| File & Folder Exclusion | File & folder path e.g.: C:example_folder or C:example_folderexclusion_01.exe |
| Process exclusion | Process name e.g: Exclusion.exe |
| Theses Actions are available: | |
| Add exclusions | |
| Import exclusions | Please note: Only one exclusion per line is allowed. A maximum of 250 exclusions can be imported. If the file contains more exclusions, it will be truncated after 250 entries. |
| Export exclusions | Exports the existing exclusions to a txt file. |
| Edit Exclusion | |
| Deletes this exclusion | |
2.4 Client configuration
| Caption | Default | Description |
|---|---|---|
| Guard | ||
| System protection | on | Basic functionality |
| PUA and PUP detection | on | Detection of potentially unwanted programs |
| System protection at system startup | on | If system protection has been deactivated, it will be automatically reactivated at the next restart |
| Use default settings for maximum file size | off | Accepts the default value (128 MB) |
| Maximum file size (in MB) | 128 | Files above this size are not scanned |
| Logging | ||
| Log system supervision in the main log | off | System monitoring results are stored in C:Program FilesIKARUSanti.viruslogguardx.log |
| Record logs for scans | om | Creates protocols for scans |
| Record all data when scanning | off | Detailed scan report |
| Overwrite logs | on | When activated, the old report is no longer overwritten with each scan but supplemented. |
| Extras | ||
| Use Proxy-Server | off | Uses a proxy server for updates |
| Use System Proxy | off | Uses the default proxy server |
| Proxyserver Address | Manual proxy server address | |
| Proxyserver Port | ||
| Proxyserver Login | off | The user name and password are only specified when the configuration is transferred. No passwords are stored in the IKARUS anti.virus portal itself. |
| Password protection | off | The password is only entered when the configuration is transferred. No passwords are stored in the IKARUS anti.virus Portal itself. We recommend that the passwords are stored in a password storage, since without a password access is not possible. |
| FastDiff | off | Real-time updates for virus patterns |
| Join reseller preview | off | To test the latest program features in advance. Only possible with licenses for verified resellers. |
2.5 Notification settings
Notifications are only sent for devices that are linked to this configuration profile via their group membership
Notification settings
| Caption | Default | Description |
|---|---|---|
| Outdated after | 28 | Number of days after which a device is to be reported as outdated. The value must be an integer! |
| Time of examination | 8 o’clock | Time at which the status ‘outdated’ is checked. |
| Recipient settings | ||
| Caption | Parameter | Description |
| Recipient | Selection or input | An existing user or an e-mail address can be defined for notifications. |
| Recipient settings | ||
| Threat found | off | |
| Security status Client insufficient | off | |
| Client not up to date | off | |
| Actions | Deletes the notifications for this recipient. | |